All articles containing the tag [
Audit
]-
How To Detect Whether Port 81 Of The Korean Server Is Maliciously Accessed And The Steps To Obtain Evidence
this article introduces how to detect whether port 81 of a korean server has been maliciously accessed, including log and traffic detection, malicious feature identification, evidence preservation and evidence collection process recommendations, which is suitable for emergency response and compliance reporting.
Korean Server Port 81 Malicious Access Evidence Collection Log Analysis Network Security Evidence Collection Steps -
Vietnam Residential Vps Application Scenarios And Restrictions For Home Broadband Nodes And Residential Ip
this article introduces the definition of residential vps and home broadband nodes in vietnam, residential ip, main application scenarios, technical and compliance restrictions, as well as deployment and selection suggestions to help enterprises and individuals make appropriate decisions.
Vietnam Residential Vps Residential Ip Home Broadband Node Vietnam Vps Node Residential Ip Application Localization Testing Bandwidth Delay Ip Ban Risk -
From Heat Dissipation To Fire Protection, Look At The Basic Requirements That Cambodian Server Rooms Must Meet
this article systematically introduces the basic requirements that cambodian server rooms must meet in terms of cooling, fire protection, power and redundancy, physical security, and operation and maintenance. combined with local climate and operational suggestions, it is suitable for the planning and management of data computer rooms in cities such as phnom penh.
Cambodia Server Room Cooling Fire Protection Data Center Cooling Ups Redundant Computer Room Construction Safety Operation And Maintenance -
How To Find Server Hosting In The United States And Take Into Account Data Sovereignty And Legal Compliance Requirements
when looking for server hosting in the united states, how to balance data sovereignty and legal compliance requirements? from data classification, hosting locations, service provider contracts to technical controls and cross-border risk mitigation, we provide systematic operational points and suggestions.
Us Server Hosting Data Sovereignty Compliance Cloudactccpahipaa Data Residency -
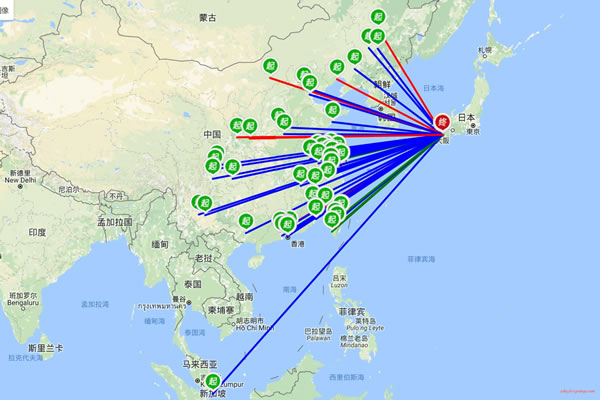
What Are The Restrictions And Suitable Groups Of Sakura Japanese Native Ip Packages?
comprehensive analysis of the common restrictions and suitable groups of sakura japanese native ip packages, covering laws, bandwidth, certification, usage scenarios and purchase suggestions, to help users make compliance and practical choices.
Sakura Japanese Native Ip Native Ip Package Ip Restrictions Suitable For The Crowd Cross-border Access Streaming Media Enterprise Testing -
German Independent Server Hosting Selection And Deployment Strategy From The Perspective Of Energy Conservation And Sustainability
from the perspective of energy conservation and sustainability, this article systematically sorts out the selection and deployment strategies of independent server hosting in germany, including data center location selection, energy sources, hardware energy efficiency, cooling solutions and operation and maintenance optimization, to help enterprises achieve a hosting solution that pays equal attention to green and high availability.
German Independent Server Hosting Energy Saving Sustainability Data Center Energy Efficiency Green Energy Cooling Optimization Operation And Maintenance Selection And Deployment -
Comparison Of Hong Kong Station Group Service Advantages And Analysis Of Key Points In Performance Expansion And Global Coverage
this article analyzes the comparison of the advantages of hong kong site group services, focusing on key points of performance expansion and global coverage, including architecture, automatic expansion, delay optimization, cdn integration and compliance security recommendations, to facilitate seo and geo optimization decisions.
Hong Kong Site Group Site Group Service Performance Expansion Global Coverage Delay Optimization Cdn Reliability Security Geo Optimization Seo -
Cambodia Vps Recommendations And Security Reinforcement Suggestions From The Perspective Of Operation And Maintenance Engineers
from the perspective of an operation and maintenance engineer, this article systematically introduces the key points for selecting vps in cambodia and practical security reinforcement suggestions, covering network, hardware, access control, system and application levels to facilitate deployment and compliance management.
Cambodia Vps Vps Recommendation Security Reinforcement Operation And Maintenance Engineer Cambodiavps Server Security Network Optimization -
How To Choose A German-made Server Brand And Performance Points Suitable For Your Business
the enterprise-oriented guide "how to choose a german-made server brand and performance key points suitable for your business" covers key considerations such as demand analysis, hardware performance, reliability, energy efficiency, security, and operation and maintenance support to help with procurement decisions and deployment planning.
Made In Germany Server Brand Performance Points Buying Guide Enterprise Server Data Center